DNS Enabler for Catalina
DNS Enabler can set up a fully-functioning Domain Name Server (DNS) on a plain Mac OS X machine. It is designed to allow a user to set up domain name information quickly using a single window, in the fastest time.
LOCALDNSANDDOMAINS is a comma separated list of local domains. If you have multiple sets of local domains intended for different DNS servers, use a semicolon to separate the various lists (this is shown in the example config file). Domains ending in.local are automatically sent to the original DNS settings of the machine. Dns Jumper v2.2 download should start automatically in a few seconds. If your download does not start automatically please click direct download link below. DnsJumper hels you to Change your dns setting easily, In some cases, you can increase the browsing speed or improve your security by replacing the DNS provided by your provider.
DNS Enabler provides the interface to allow users to specify domain name-to-address mappings for machines on the Internet, as well as their aliases or MX records (e.g., which machines act as mail servers for the domain).
Additionally, it allows users to set the other domain and zone information, e.g., Time-To-Live Intervals, that determine how long these information remain valid.
It will automatically generate the named.conf file, the forward mapping files for each domain, the reverse mapping files for each network, and all the resource and reverse pointer records.
Upgrade Notes, if you’ve used DNS Enabler before and didn’t do a clean install of Catalina:
Once you have launched the latest version of DNS Enabler, save the current config using the File->Save menu item, do a De-Install from the Help menu, which removes all the previous cruft, and then quit and come back to the app. You'll then get the config files, libraries and the other stuff that will work with Catalina.
Dns Jumper For Mac Catalina Free
Please note that the Bonjour configuration panel has been left out of this release of DNS Enabler.
Introduction - a Basic DNS Configuration for the Local Network
DNS Enabler on a private local network
Scenario - imagine that you've set up a local network behind a router or an Airport Base Station, e.g., for doing testing or web development.
Let's say that the local network is on subnet 10.0.1.x and you've decided to have a web server, a mail server, and an ftp server on a static IP address 10.0.1.201, plus other servers on 10.0.1.202 and 203. To simulate real world conditions and not have to change your code when you move to a production environment, you want to access the servers via domain names, e.g., lifeassets.com, as shown above.

So this is what you do. You run DNS Enabler on the 10.0.1.201 machine and set it up as shown.
Important Note : On the machine that you're running DNS Enabler, the DNS Server setting in Network Preferences should always point to itself.
You can now point all the other machines on the local network to use 10.0.1.201 as their name server (via the DNS Server setting in their Network Preferences). This way, all the local machines can now access the mail, web, and ftp servers via their domain names. If you've also set up an alias like www for the main server at 10.0.1.201, you can also hit that server by typing something like www.lifeassets.com into a web browser.
This is a simple thing to do and it takes only a couple of minutes to set up, but it can be made even more useful. For example, you may have a few other machines containing projects at various stages of development. You can switch your machines around and test each machine in turn as www.lifeassets.com, say, just by changing the name-address assignments in DNS Enabler.
Or, since this is a private local network, you can simulate more than one domain, e.g., to test the effect of sending mail from one server to another, say, from roadstead.com to cutedgesystems.com. You can set up DNS Enabler as shown here:
Another Scenario : This happens quite often - you may have set up a web or mail server behind a router, broadband modem, or wireless base station when you noticed that machines on the local network cannot 'see' the server via its domain name, while machines outside the network can (e.g., you've used dyndns.org or some such service to obtain your own domain name).
In this case, you can use DNS Enabler to broadcast the domain name to all the local machines (using the simple configuration outlined above) and help them find their way to your server.

A Configuration for the Public Network
DNS Enabler on a public network. Introducing MX records.
An example company, Kemper, has been given a range of 64 public IP addresses from 203.116.189.129 to 203.116.189.192. It sets its DNS server at 203.116.189.130 and gives it a name, pridns.kemper.com.sg. Its backup secondary name server is at the ISP, secdns.cyberway.com.sg.
The machine that runs the name server is also the mail server and ftp server. Therefore, we give it the aliases, mail and ftp. We also add the label MX to indicate that pridns.kemper.com.sg, alias mail.kemper.com.sg, is providing the mail service for the domain kemper.com.sg.
Note : If we have a host with the same name as the domain, and we run the mail server on this host, we won't need to set up an MX record.
If we have a secondary backup mail server among our machines, say at backup.kemper.com.sg, we can assign it by adding the MX label to that machine. The number in the bracket, as in MX[10] and MX[20], denotes the precedence.
Across the firewall from the public network, the company runs a private local network (in the 192.168.0.x range). DNS Enabler can handle the setup of the name service for this local network within the same window. Because it is a private network, it can be given any domain name, which we enter into the Virtual Domains field. In our case, we use local.com, and we have two servers, accounting.local.com and keystone.local.com, that are used (and seen) only by the local users.
MX records :
If our ISP provides us with a backup mail server in case our whole domain is down, we can specify this backup mail server, as in the example above (with its IP number denoted by a dash - since we probably wouldn't know its physical address) :
This is how our MX records will be ordered :
kemper.com.sg IN MX 10 pridns.kemper.com.sg.
kemper.com.sg IN MX 20 backup.kemper.com.sg.
kemper.com.sg IN MX 30 mailHost.cyberway.com.sg.
Advanced Configurations
The following screenshot shows DNS Enabler handling the data entry for the domain described in Paul Albitz and Cricket Liu's DNS and BIND book. It shows computers on two networks, 192.249.249.x and 192.253.253.x, for the domain movie.edu, with the router between the two networks at 192.249.249.1 and 192.253.253.1. The router is given the name wormhole.movie.edu, alias wh.movie.edu and serves as a backup for the primary name server terminator.movie.edu while providing the name service for the 192.253.253.x network. [Download the configuration, here, and open it in DNS Enabler].
Two other computers have aliases - terminator.movie.edu, which is known as bigt.movie.edu, and diehard.movie.edu, also known as dh.movie.edu.
wh249.movie.eduand wh253.movie.edu are private interface-specific names used by the administrators and the dashes in the Alias column signals to DNS Enabler not to create reverse pointer records for them in the zone file.
In the example above, DNS Enabler should be installed on the machine named terminator.movie.edu, which is the primary name server for the domain movie.edu. When you hit the Start DNS button, DNS Enabler will read in the name-address mappings, start up name services so that other computers can get answers to these name-address queries (and keep these running across reboots).
DNS Zone Files
This is the zone file created by DNS Enabler for the above configuration:
$ORIGIN .
$TTL 10800
movie.edu IN SOA terminator.movie.edu. bernard.movie.edu. (
2006020703 ; Serial
10800 ; Refresh
3600 ; Retry
604800 ; Expire
86400
)
NS terminator.movie.edu.
NS wormhole.movie.edu.
$ORIGIN movie.edu.
localhost A 127.0.0.1
robocop A 192.249.249.2
terminator A 192.249.249.3
bigt CNAME terminator.movie.edu.
diehard A 192.249.249.4
dh CNAME diehard.movie.edu.
misery A 192.253.253.2
shining A 192.253.253.3
carrie A 192.253.253.4
wormhole A 192.249.249.1
wh CNAME wormhole.movie.edu.
wormhole A 192.253.253.1
wh CNAME wormhole.movie.edu.
wh249 A 192.249.249.1 ; interface specific name
wh253 A 192.253.253.1 ; interface specific name
DNS Enabler will also create the reverse pointer records.
What about MX Records, TXT Records, and Forwarders?
The following picture shows how you would handle MX and TXT records and Forwarders for the domain movie.edu :
misery.movie.edu and shining.movie.edu are the mail servers for the domain movie.edu, with misery.movie.edu ranking higher in priority as the target to receive mail for the domain. The Mail eXchanger role that both of these machine perform are denoted by the MX[xx] notation.
You can leave a note that shining.movie.edu, the backup mail server, is located at the math lab by adding a TXT[string containing a description] label to the shining.movie.edu record.
There is a new spam-fighting movement involving the use of SPF records (SPF = Sender Policy Framework). These are used in conjunction with TXT records kept at your DNS Server. In this case you would add a TXT[v=spf1 a mx ~all] record to the machine acting as your site's mail server.
Forwarders are useful if you need to shunt name resolution to a particular external name server. e.g., your ISP's, to keep off-site search for domain name resolution to a minimum, so as to improve network traffic. In the example above, 192.249.249.11 and 192.249.249.13 are the site's forwarders, and you list them in the Forwarders field, separated by commas.
The configuration, above, can be downloaded from here. The zone file that DNS Enabler produces from that configuration is shown below :
$ORIGIN .
$TTL 10800
movie.edu IN SOA terminator.movie.edu. bernard.movie.edu. (
2006020704 ; Serial
10800 ; Refresh
3600 ; Retry
604800 ; Expire
86400
)
NS terminator.movie.edu.
NS wormhole.movie.edu.
MX 10 misery.movie.edu.
MX 20 shining.movie.edu.
$ORIGIN movie.edu.
localhost A 127.0.0.1
robocop A 192.249.249.2
terminator A 192.249.249.3
bigt CNAME terminator.movie.edu.
diehard A 192.249.249.4
dh CNAME diehard.movie.edu.
misery A 192.253.253.2
shining A 192.253.253.3
shining TXT 'location: math lab'
carrie A 192.253.253.4
wormhole A 192.249.249.1
wh CNAME wormhole.movie.edu.
wormhole A 192.253.253.1
wh CNAME wormhole.movie.edu.
wh249 A 192.249.249.1 ; interface specific name
wh253 A 192.253.253.1 ; interface specific name
Actually, you can set up quite complicated MX and CNAME record combinations, like that shown below :
Dns Jumper For Mac Catalina Os
where you can set up an alias record for your domain, like testApp.yakcat.com above, that actually points to apple.com (i.e., it's a CNAME for apple.com) and googleffffffffd07f4431.yakcat.com is a CNAME for google.com.
The example above also shows how you can indicate to the DNS system that an external mail host (mailstore.secureserver.net) is providing mail services for two machines in separate domains under your care, where one of them is the main domain, yakcat.com (you can leave out the domain name in the MX[10] specification, if that is for the main domain), and the other is calvary.org (which has a fall-back mail server provided by calvary.com).
IP Addresses in CIDR Format
DNS Enabler now allows you to enter IP addresses in CIDR format, e.g. if your ISP has delegated control of a sub-block (or two) of addresses to your name server and you need to create reverse pointer records in CIDR format so that when other mail servers do a reverse name lookup on your IP addresses, your name server will return the correct answers.
The picture below shows how CIDR-type addresses can be entered :
DNS Enabler can handle the general case where more than one block of IP addresses in the same sub-net can possibly be delegated to your name server.
This is how DNS Enabler will create the reverse pointer records :
A reverse lookup on the IP address 12.53.154.35 will go first to the root servers which then pass the query on to the ISP name server that is known to control the address range that 12.53.154.35 sits in.
Having delegated a sub-block from of IP addresses (from 12.53.154.32 to 12.53.154.39 to you (which is what 12.53.154.32/29 really means), the ISP will re-direct that query on to your name server, whose job is to say which host name was mapped to that particular position 35. In this case, your name server's answer would be 'smtp.domainName.com'.
A normal lookup of the name 'smtp.domainName.com' will still work correctly as DNS Enabler would have created the name-to-IP address mappings as usual :
So with things set up this way, a suspicious destination mail server will have its checks confirmed that your smtp server is really what it purports to be, which is (probably) what this whole exercise had been meant to serve.
Setting up a Secondary Name Server
DNS Enabler also allows you to set up a secondary slave name server. In the example below, besides running DNS Enabler on the Primary Name server, terminator.movie.edu, you can also install it on a Secondary Name Server, wormhole.movie.edu.
First, use the Save menu item in the File Menu on the Primary Name server, to make a copy of the configuration. Then copy this to the machine that will act as the Secondary Name Server (in our case, wormhole.movie.edu).
Run DNS Enabler on this secondary machine, and use it to open the configuration you've just copied over.
Then click on the radio button next to the label 'Secondary Name Server' :
When you hit the Start/Restart DNS button, wormhole.movie.edu will now run in slave mode. It will monitor the zone files for updates coming in from the primary server. So when you make a change to the primary server (terminator.movie.edu in our example), you will see the change show up automatically on the screen of the machine running the secondary server.
Network Notes : You need to make sure that the network set up is correct, i.e., both servers must be able to access (or 'see') each other. Also, on each machine that you're running DNS Enabler, make sure that its DNS Server setting in Network Preferences points to itself.
DNS Enabler can also set up multiple secondary slave name servers for a single primary name server. Just enter the list of slave server host names into the Secondary Name Server field of the machine acting as the primary server and this will tell the primary name server to notify all of these secondary servers whenever there is a change in the zone data that it is managing and it will transfer these updates to the slave servers automatically.
Support for Dynamic DNS Updates
DNS Enabler will allow client host machines with dynamically assigned IP addresses (or machines on the move) to update the DNS Server automatically with their latest IP address, keeping their domain name-to-IP address mapping in sync at all times.
To set up the DNS Server to listen to DNS update requests coming in from dynamic DNS clients, click on the 'Allow Dynamic DNS Updates' check-box, below :
A dynamic DNS client, whose host name-to-IP address mapping is tracked by the DNS Server above, needs to run a special piece of software that will monitor the state of its IP address for changes. This service is provided by a companion application to DNS Enabler called DNS Agent for Catalina. Whenever the IP address changes, DNS Agent will call home to the DNS Server to update it with the latest value.
In order to establish that it has the necessary authorisation to update the DNS Server, the DNS Agent needs to have an authorisation key installed that it has obtained from the server.
Transferring the Authorisation Key to DNS Agent is very simple. Click on the question mark icon next to the 'Allow Dynamic DNS Updates' check-box. It'll open up the dialog box, below, which provides more details about the way dynamic DNS updates work, as implemented by DNS Enabler :
Drag the Authorisation Key, as represented by the icon on the bottom-right hand corner of the dialog box, to the machine running DNS Agent, whose IP address is being tracked. You can drag the key file to the server's desktop and transfer it to the client machine via file-sharing or via email.
Once on the client machine, if you have the DNS Agent application there, you can simply double-click on the key and it will open the DNS Agent app. Save the key and follow the instructions on the DNS Agent web page. In a couple more steps (which involves entering values for the address of the DNS Server and the host name you are updating for), you are done, and you can quit the DNS Agent, which leaves a daemon running, even across shut-downs and reboots, that will always update the DNS Server with that client's current IP address.
If you leave the DNS Enabler application on in the server, you can see the IP address updates appearing automatically, but a few minutes late (say, 10 minutes later). Why so late? This is because the updates are cached by the server but not written to disk straightaway, in case a lot of updates come in at the same time. But they're registered immediately by the server, and you can check that it's true if you do a dig on the server in Terminal. The zone files are batch-updated later. When they do get updated, you'll see that reflected on the DNS Enabler interface immediately.
Bonjour Wide-Area Services
The Bonjour panel allows DNS Enabler to be used as a configurator for Bonjour services, to enable wide-area discovery of Bonjour devices :
More information about the types of Bonjour services you can currently configure, and what you need to enter into the individual columns in the Bonjour panel, can be found at : http://www.dns-sd.org/ServiceTypes.html e.g., DNS SRV (RFC 2782) Service Types.
What DNS Enabler saves the user is the need to know the specific syntax to set up SRV and TXT records at the DNS server. All he needs to know is the Bonjour service type, e.g., _http._tcp for publicising web pages (that may be served even from local private networks - you can use the Port number field to publicise a different port other than 80 and port-map that incoming request to a specific local machine) and the domain that will serve that request. The service name is a label that will show up in the Bonjour menu in, say, Safari. And the TXT column contains the path to that specific web page. (The TXT column stores different things for different services. See the cited Bonjour reference).
The Log Panel
The Log Panel shows the contents of the DNS Server log file at /Library/Logs/named.log, in reverse order, with the latest entries listed first. It also shows the current version number of the name server.

DNS Enabler will rotate the logs when it gets too big and keep up to 5 previously archived versions of the log file.
De-Installing DNS Enabler
You can de-install DNS Enabler by using the last menu item in the Help menu. It will shut down the DNS Server, if it is running, and remove all files installed by DNS Enabler.
DNS Enabler works from its own folder in /usr/local/cutedge/named, in which are stuffed the named.conf and the db files used by DNS Enabler. DNS Enabler leaves your system in its original state after de-installation.
Release Log
13.0 October 13th 2019. DNS Enabler for Catalina released. The current named/BIND binary bundled into DNS Enabler is BIND 9.14.5
A DNS cache or DNS resolver cache, is a temporary database of DNS lookups on the OS and browser. It consists of the records of recent as well as attempted visits of websites along with domains. To troubleshot cache poisoning or other internet connectivity issues, you may need to flush the DNS cache. The action will remove all the DNS entries. Besides, it also gets rid of invalid records. Let’s check out the way to clear the DNS cache on your Mac.
What does Clearing the DNS cache do?
If you are having trouble accessing a website on your Mac, or if webpages do not load properly, clearing DNS cache will help. It also lets you correctly see the new version of a website, in case the site has recently moved its servers. It does so by clearing the outdated entries and fetching the new ones. Finally, regularly flushing DNS cache may also help in hiding search behavior and offer security against manipulation.
How to Flush DNS Cache on Mac
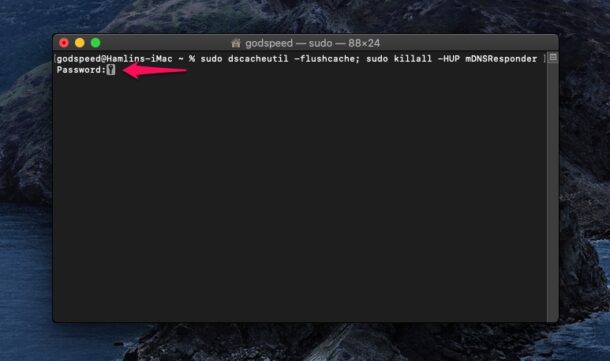
For macOS Catalina, Mojave, High Sierra, Sierra, and macOS El Capitan the command is the same.
- Open Terminal using Launchpad or Use Finder → Applications → Utilities, or Spotlight Search (Command+Space Bar) for this.
- Now, you need to enter the command given below.
sudo killall -HUP mDNSResponder - Enter your Mac’s password and then press the enter key again.
Done! Now, you may have to wait for a few moments until the DNS cache is completely flushed out. Once it’s done, a verbal audio alert will confirm that the DNS cache is flushed on your Mac.
You have successfully cleared the DNS Cache on your Mac! Most likely, now you will have no trouble visiting websites or seeing webpages.
Clear DNS Cache in Older macOS versions
If you are using an older version of macOS, then here are the commands for those.
To clear DNS cache on macOS Yosemite, enter the following syntax:
sudo discoveryutil udnsflushcaches
To clear DNS cache on macOS Lion, Mountain Lion, and Mavericks, enter the following syntax:
sudo killall -HUP mDNSResponder
That’s all, folks.
Signing off…
Hopefully, getting rid of the DNS cache will no longer be a big deal for you. Additionally, if you like, you can also choose to clear DNS Cache only for the Google Chrome browser. For this enter chrome://net-internals/#dns in Chrome’s address bar. Next, click on Clear host cache.
You may also like to check out:
If you have any questions related to this, please toss it up in the comments below.